Introduction to Broadband and Convergence
What is Convergence?
Pros and Cons of multiple bearers and devices
Now that we understand critical communications more clearly, we can better appreciate some of the advantages and issues surrounding the use of multiple bearers and multiple devices.
At first glance, running multiple bearers may seem inefficient. Why not have just radio or just cellular to carry communications services?
The short answer is that each bearer has some advantages and some disadvantages. Each differs in functionality, range, reliability, availability, equipment options, power consumption, cost and security. With multiple bearers at hand, an organization can tailor its communications deployment to meet the business requirements of each part of its operations.
For instance, no single technology can provide communication across the varied terrain, fluctuating demand, and escalating data usage that system designers must consider. Coverage holes inevitably appear, which can be mitigated if multiple bearers with different coverage characteristics are employed.

Reliance on a single technology also creates risk. Disasters and national emergencies often result the overloading of public cellular networks and jam communications. Adding multiple bearers provides redundancy to critical communications. For example, the 2005 London underground bombings overloaded the cell phone systems, but LMR radio in the buses provided alternative communications channels for London Transport. For critical infrastructure, such as a power utility, regulators may require a separate auxiliary communications network to back up the primary system in case of failure.
And sometimes it just makes sense to add a bearer to gain new capabilities. However good LMR was at providing voice communications, other bearers were needed to access broadband data services.
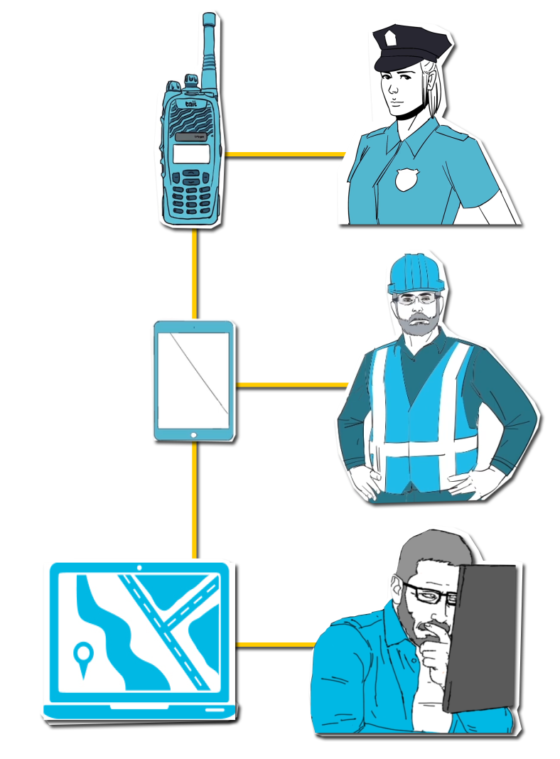
A single-bearer communications system also restricts the choice of devices for your staff. There are relatively few organizations running critical communications networks that can get by with only one or two types of comms terminal. Some sections of an organization may need big displays and robust keyboards, while other departments are happy with cellphone displays and touchscreen input. Field handhelds are usually ruggedized, often intrinsically safe, and may sport noise-cancelling microphone headsets while office comms sets can dispense with these features.
It makes commercial and operational sense to let the diverse work requirements drive the choice of bearers and devices rather than force a solution based upon what can be achieved and is available within a single technology.
Smarter communications solutions can be conceived through the integration and management of multiple technologies and the devices they support.
In real life, however, integrations of multiple bearers usually don’t go far enough. Critics of such hybrid systems say – with some justice – that these are not really coherent systems. Instead what we have is a collection of communications subsystems that appear internally integrated but are in fact managed separately and are only loosely connected.
Getting them to work together is both complex and costly. How do you coordinate overall performance or monitor security or administer consistent access control? There is a fundamental issue here about system integration and management – this issue is addressed by Unified Critical Communications.
 Radio Academy
Radio Academy