Introduction to P25
Call Types and Features
Introduction to P25 Encryption
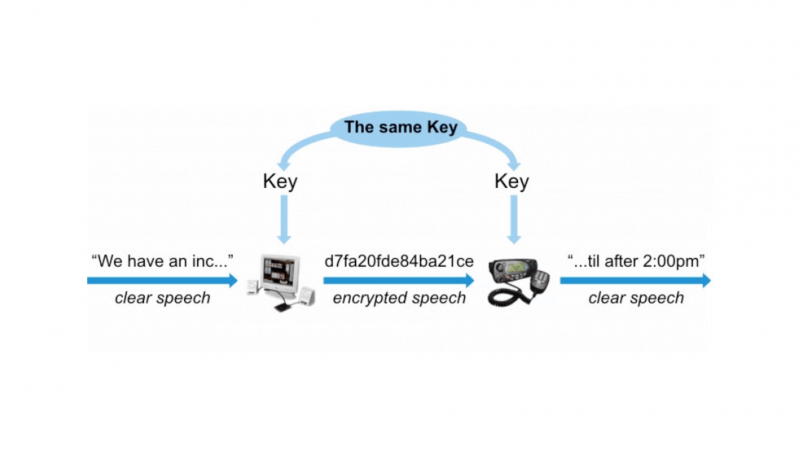
Encryption in radio communications enables secure communication between parties and is achieved by loading the same key into all radios in a group.
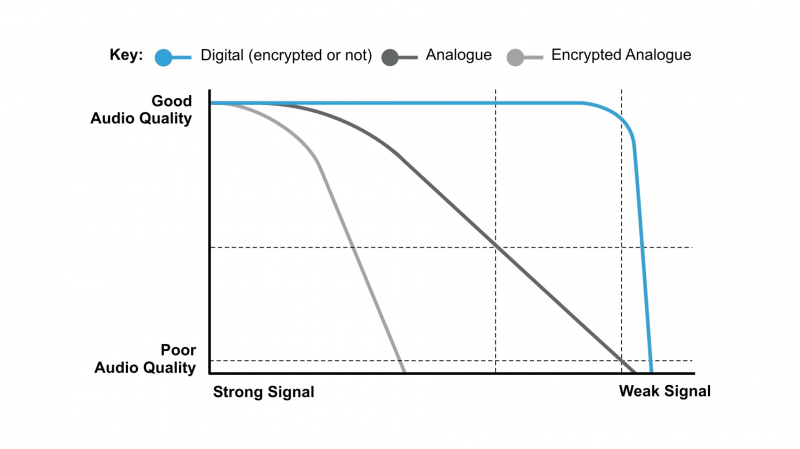
The key is like a secret number or password that must be known in order to decrypt the call. Radios in their group can then talk amongst each other privately, and no outsiders can intercept the communications. Although analog encryption is possible, this typically degrades the audio quality and also results in a reduced coverage area, as stronger RF signals are needed to clearly receive the encrypted calls.
One of the key benefits of P25 Digital Radio over analog radio is the ability to securely encrypt calls without impacting the coverage area.
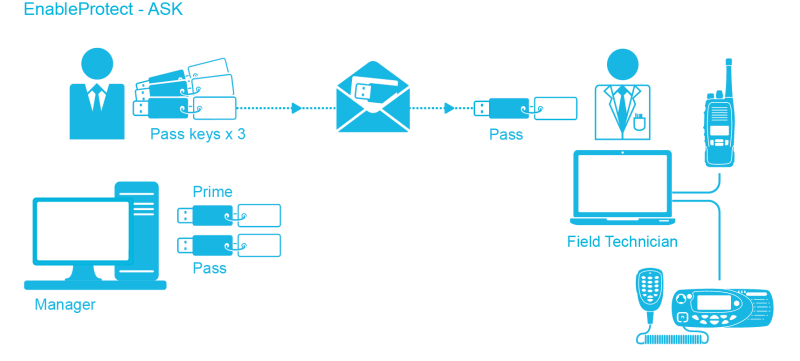
Enabling P25 encryption is easy. A channel or group is programmed to use encryption and a key is loaded into each radio that uses that group.
DES uses a 56-bit encryption key and AES uses a 256-bit encryption key. The type of encryption to use depends on the type of information you’re protecting.
AES is a more secure form of encryption, however maintaining the security of that channel is more complicated.
Policies and procedures will need to be put into place to determine who is allowed to access the secure channel. In addition, plans will need to be in place to determine what to do if a radio with the key is lost or stolen. Often this is easily managed by having more than one encryption key.
Tactical teams that require a higher level of security may generate their own encryption keys for specific operations. They can tightly control or manage those radios, and have an up to date knowledge of their current status. A different key is used to encrypt general day-to-day communications and is available to a wide group of people.
Because a large group of people have access to this channel and the key, it is considered to have a low-level security. If the radio is lost, it could take some time for this to be reported and disabled. And replacing the key and all of the radios will be a time consuming, costly exercise and may only happen on rare occasions.
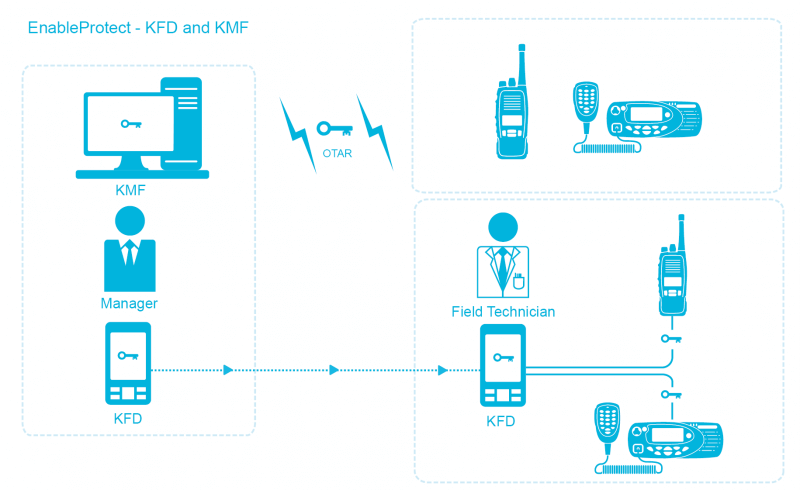
Larger systems may use a feature called over the air rekeying, or OTAR. This allows the updating of the key over the air and dramatically simplifies the process of rekeying the radios in the field. You do not need to physically touch each radio to load the key with a key-loader. However, OTAR still has an administration overhead to track down and follow-up on any problem radios that could not be rekeyed. This is common where multiple shifts, spare radios, and specialist vehicles mean radios are not powered on and active on the radio system all of the time.
In summary, P25 makes it very easy to add encryption to a radio system. However, it is important to have a good plan in place to ensure communication stays secure and the administrative overhead of managing the radios is in line with the level of security required.
This concludes our introduction to P25. We hope it was helpful for you.
If you’d like to contact us please follow the link below or post in the P25 forums.
 Radio Academy
Radio Academy